Pick your favorite quote for today!
What would you do if you were stuck in one place, and every day was exactly the same and nothing that you did mattered?
… or rather:
Welcome to Adventure!! Would you like instructions?
Wed Feb 2 22:22:22 UTC 2022 Slackware 15.0 x86_64 stable is released! Another too-long development cycle is behind us after we bit off more than we could chew and then had to shine it up to a high-gloss finish. Hopefully we've managed to get the tricky parts out of the way so that we'll be able to see a 15.1 incremental update after a far shorter development cycle.
 I honestly kept my breath and have had some difficulty believing that this would eventually really happen, but yet here it is. Slackware 15.0 stable! Released yesterday and available on mirrors across the globe today.
I honestly kept my breath and have had some difficulty believing that this would eventually really happen, but yet here it is. Slackware 15.0 stable! Released yesterday and available on mirrors across the globe today.
I am fiercely proud of Patrick Volkerding who has again showed all of us that the oldest actively maintained Linux distribution is more than a rolling release for Linux enthusiasts.
The latest stable release 15.0 is packed with applications for both desktop and server usage. It is truly a modern Linux platform that power users can and should embrace as their daily driver.
I will share with you some of the highlights and particulars of the development process between the release of Slackware 14.2 (the previous stable) and the new 15.0.
- With five years and seven months in the making, this has been the largest interval between stable releases.
- We said ‘farewell’ to the Slackware Store and goodbye to printed DVD and CDROM sets.
A major reason for this dragged-out development cycle is the realization that for a long time, Pat and family have been deprived of substantial amounts of revenue which the people of The Store reaped through the sales of Slackware installation media, clothing and other paraphernalia. The truth was shared by Pat in a post on LinuxQuestions and resulted in a long-running thread discussing how the community could help with the funding: https://www.linuxquestions.org/questions/slackware-14/donating-to-slackware-4175634729/ .
Luckily a new means of securing an income for Pat was established through Patreon, which allows Pat to focus again on his Slackware distro. After all, Slackware is his only source of income; the rest of the coreteam have regular day jobs and we don’t get (nor want) any part of the revenue. - A ChangeLog.txt of roughly 40,000 lines makes the process of “slackpkg install-new” (churning through all that text) to find all those added packages a long and painful one.
- The Slackware 15.0 core distribution consists of 1590 packages, a 19% increase from the 1332 packages in Slackware 14.2 core (i.e. everything not in ./extra or in ./testing).
A lot of packages have been removed (276), many of those belong to KDE4 and 82 of them are the old language packs. You won’t miss a thing there because language support in Plasma5 is now included in all the application packages.
If you look at the number of packages that have been added to the distro (i.e. did not exist in Slackware 14.2), that’s an impressive 534. - The compressed size of these packages went up from 2.4 GB to 3.0 GB. Uncompressed and installed onto your computer, the difference will be significantly larger. The recommended disk space needed for a full installation, increases from 9+ GB (Slackware 14.2) to 16+ GB.
So what about that exciting content you can find in the new 15.0 release?
- Slackware 15.0 installs Linux kernel 5.15.19.
- The kernels all have preemption enabled and you can configure your bootloader for full, dynamic or no preemption.
- The installer properly supports installing to NVMe disks and has improved support for installing on UEFI platform.
- Slackware still supports 32bit hardware platforms and is one of the few relevant Linux distros that do so today.
Both the 64bit and the 32bit distro are built from a single source tree. - Collaboration with smart people on the LinuxQuestions.org forum resulted in the ability for Slackware to be reliably built from scratch these days. Thanks in particular to worsel and nobodino. The latter maintains his efforts in a git repository from which Slackware has borrowed several patches. Slackware itself has a ‘master build script’ called make_world.sh and Patrick keeps a log of everything that “fails to build from source” aka the FTBFSlog files which you can find in the source-directory root of every package series. Nothing in the distro fails to build from source right now, which is awesome and a definite change from previous stable releases.
- In ./source/installer you find the complete sources to easily rebuild the Slackware installer from scratch.
- ConsoleKit2 was replaced with elogind as the session/seat manager. Elogind is a standalone version of the logind code in systemd and independently maintained at https://github.com/elogind/elogind .
- FFmpeg and Lame have been added to the distro, yay! Also, it includes SDL2, speex, opus, fluidsynth.
- A new command-line ISO creation tool to supplement cdrtools was added: xorriso.
- Python3 was introduced but Python2 stuff remains available and is still the default python. Its most relevant modules have been bundled in a compatibility package.
- Postfix has been added and Sendmail moved to ./extra where it still receives upgrades. Lucky me, I still prefer and use Sendmail on my boxes.
- Dovecot is the powerful new IMAP and POP3 server, replacing the old imapd and ipop3d.
- The Qt4 graphical toolkit has been removed and Qt5 came in its place.
- KDE 4 (which was already abandoned at the release of Slackware 14.2) has been replaced with KDE Plasma5. More specifically, with Frameworks 5.90, Plasma 5.23.5 and Applications 21.12.1, meaning the very latest versions; all released this January 2022. This is topped with some cool additional Plasma5 applications like the Calligra office suite, Krita vector drawing program, Digikam photo management, KMymoney personal finance management, the Chromium- and Qt5-based webbrowser Falkon and Kyle LaTeX editor (and then some). And of course KDevelop.
- The latest XFCE 4.16 is included and it’s a very nice step-up from the version of Slackware 14.2.
- Wayland 1.20.0 is available as alternative to the venerable X.Org 1.20.14 which is still the default graphical display system.
- The latest Mesa and Vulkan libraries are installed and GLvnd (the GL Vendor-Neutral Dispatch library) ensures that for instance NVIDIA’s binary driver is a breeze ti install and will not overwrite any system files.
- Pulseaudio has competition from Pipewire which has been added to the distro and ships with a configuration that can mostly replace pulseaudio with this new low-latency audio server.
- The whole build toolchain has seen a thorough refresher, with glibc 2.33, GCC 11.2.0 and LLVM 13.0.0 and the addition of Rust which is now at 1.58.1. Also essential tools that are part of modern-day software compilation like meson, ninja, scons and icecream are new in Slackware 15.0.
- … and there’s a lot of other stuff that you have to find out for yourself.
Using Slackware
All in all, when you install Slackware 15.0 on your computer you will be able to work in graphical desktop environments and using tools that are on par with all the big distros. When looking for software that is not part of the core distro you can turn to slackbuilds.org (SBo) which is a curated platform for Slackware package build scripts. Tools like sbopkg, sbotools and slpkg will assist you in automating the build- and dependency resolving process when using these scripts from SBo.
Third-party package repositories are also available to quickly install binary packages if you do not trust yourself when compiling from source. You can think of my own alien and restricted packages but also Robby Workman’s package repository or the SlackOnly collection of packages that have been pre-compiled for you out of all the SBo scripts.
Slackware’s own slackpkg package manager which only deals with official Slackware packages can be extended with the plugin slackpkg+ if you want to be able to easily manage a mix of official and 3rd-party packages using a single tool.
Slackpkg with the slackpkg+ plugin also supports managing a multilib installation (i.e. a 64bit Slackware OS which is capable of running and compiling 32bit software). With multilib, running the Steam gaming platform is fully supported on your 64bit Slackware, and Steam applications run as fast on Slackware (or faster) than on Windows.
I hope you are all as excited about this new release of Slackware Linux as I am, and I hope you will have a lot of fun using it. Of course, those of you who have been running the ‘bleeding edge’ all the time, aka Slackware-current, can keep doing that. The Slackware-current tree is still there and it will now focus on post 15.0 development towards the next stable release.
Upgrading from 14.2
People upgrading from Slackware 14.2 have multiple options. You should definitely read the CHANGES_AND_HINTS file to get a good picture of the many package additions and removals. The UPGRADE.TXT file is an invaluable source if you want to perform a manual upgrade.
The Slackware Documentation Project contains an article called “upgrading Slackware to a new release“. It describes how to use the slackpkg tool (which is part of Slackware) to perform the upgrade with a large degree of automation.
Still, it is good to be aware that Slackware moved from ConsoleKit2 to elogind and one thing will be immediately obvious if you start an X session after upgrade and reboot:
With elogind as the session/seat manager instead of ConsoleKit2, if you run ‘
startx’ or ‘startkwayland’ at the console, you won’t see a VT (virtual terminal) switch. In the past, your console TTY would usually be tty1 but your graphical session would start on tty7 and you would automatically be switched from tty1 to tty7. This is no longer true – the graphical session will re-use your console TTY.
You can read more details about the implications of the switch to elogind in my 2020 blog post here on Alien Pastures.
Get Slack
Download your official ISO images from any of the Slackware mirrors. We use mirrorbrain to ensure that a visit to mirrors.slackware.com will lead you to a server that is near to you.
Support Slackware
Please consider supporting Patrick and his family by visiting his Patreon Page, choosing a membership category and becoming a Patron. If you can spare a dollar or so per month, it will help keeping this unique distribution alive. All that money goes only to Pat.
If you are longing for the stuff that The Store used to sell, you can have a look at this CafePress URL which is Pat’s. Anything you buy there generates some money for him: so on you go to Patrick’s CafePress Shop.
Don’t fall for the fakes (several others on Cafepress sell clothing and gear with Slackware’s logo on them)!
Give Slackware a test-drive
Has the article made you curious or interested but you don’t yet feel comfortable installing Slackware on your computer?
We’ve got you covered!
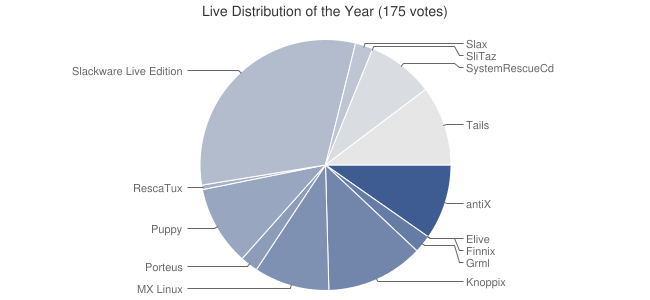
There’s a Slackware Live Edition waiting for you. It is the same Slackware 15.0 but it will run entirely from a USB stick, won’t touch your harddisks and you don’t have to install anything.
Unlike Slackware itself, the Slackware Live Edition supports Secure Boot but you’ll have to enroll the liveslak certificate into your computer’s MOK first.
And if you do want to install Slackware after seeing the Live Edition, there’s a “Install Slackware” icon right there on the graphical desktop, which you can click (and use the password “live“!) to run through a slightly modified but still very familiar Slackware setup program (called ‘setup2hd‘ in the Live Edition).
Get the ISO for Slackware Live Edition 15.0 here: https://slackware.nl/slackware/slackware-live/slackware64-15.0-live/ (rsync via rsync://slackware.nl/mirrors/slackware/slackware-live/slackware64-15.0-live/). Instructions about installing the ISO to a USB stick and using Slackware Live can be found at https://liveslak.org/ or https://docs.slackware.com/slackware:liveslak#enduser_documentation .
Choosing development or stable
Slackware comes in two flavors:
- The stable releases (14.2 and 15.0 being the most recent ones) which get regular security updates but no changes in functionality;
- And the development release called ‘slackware-current’ which has a lot of activity with sometimes daily updates, new functionality and basically being there for all of us to test and find the bugs.
Note that the designation ‘-current‘ confuses some people who interpret “current” as “latest stable“. It is not!
Are you running ‘-current’ but want to switch to Slackware 15.0 and enjoy a stable experience with regular security updates but without the hassle of daily upgrades and occasional breakage? It’s as easy as opening the mirror list (/etc/slackpkg/mirrors) for your package manager slackpkg, and selecting a Slackware 15.0 mirror instead of a Slackware-current mirror.
To give an example: I myself would change the single un-commented line in that file “http://slackware.nl/slackware/slackware64-current/” to “http://slackware.nl/slackware/slackware64-15.0/“, and then run “slackpkg update ; slackpkg install-new ; slackpkg upgrade-all“. Now my computer is fully up-to-date with Slackware 15.0 and ready to receive future security upgrades.
Note that if you are not only interested in security updates but actually want to be able to run new software all the time, then the development release “Slackware-current” is still the better option for you; but you need to be able to fix the occasional breakage which is inherent to walking the bleeding edge. If you want to switch from a stable release to -current, the process is simular to the example above: change the mirror line in “/etc/slackpkg/mirrors” to the URL of a slackware-current repository and be sure to read the documentation.
Looking forward
Things I hope to see in that next release post 15.0:
- Out-of-the-box support for SecureBoot
- The switch from Elilo to Grub as the default bootloader for UEFI platforms
- Getting rid of the huge kernel and automatically generate and use initrd.gz images with generic kernels in Lilo and Grub
- Full integration of Pipewire as an audio/video server replacing Pulseaudio and making Jack2 superfluous
- A basic firewall as part of the initial installation
Not all of that will probably be achievable, but we’ll see…
In memoriam
A long-standing member of the Slackware core team passed away during the development process towards Slackware 15.0. Erik Jan Tromp (alphageek) would have loved to have been able to witness the release of Slackware 15.0 but circumstances decided otherwise. We said goodbye to him in March 2020.
He will be remembered fondly.



Recent comments