 Finally! I have a working package for Calibre 5.38.0, targeting Slackware 15.0 and -current.
Finally! I have a working package for Calibre 5.38.0, targeting Slackware 15.0 and -current.
As you surely know by now, Calibre is an e-book library management program, probably the best you can get and it surpasses its commercial rivals in terms of feature set and ease of use.
Calibre is not only a library manager, it can act as a content server to make your book library accessible online (on your phone and in web browsers for instance), and it also contains a Qt5-based e-book reader application, as well as a full-fledged e-book editor. If you have online magazine or newspaper subscriptions, Calibre can download these magazines automatically for you and add them to your library.
It is also quite the complex piece of software. It is written in Python, using several modules to enable its features. Calibre creates its graphical user interface using PyQt5 widget libraries. My calibre package for Slackware embeds all these modules, so that the package does not have any external dependencies. It does expect a full Slackware installation however, because that includes Qt5, PyQt5 and related packages. You could slim down your Slackware as long as you keep Qt5 related packages installed.
It took a long time to upgrade my Calibre 4.x package to 5.x, the first release in the 5.x series was on 25 September 2020. The reason is that the developer, Kovid Goyal, switched Calibre from Python 2 to Python3 and that influenced many of the Python modules that are used by the program. I had decided to wait for a Slackware 15.0 release to start working on the calibre.SlackBuild… but then that Slackware 15.0 release got delayed, and delayed, and… I could finally free up some of my time to actually do this, last week.
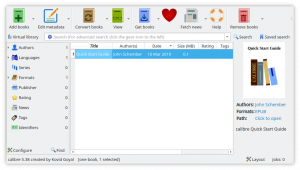
So here it is: Calibre 5.38.0, get it from my repository or any mirror (like my own US mirror)!
Note that you should either install my calibre4 package, or calibre (now at 5.x) but do not install both at the same time! Their files overlap.
Another note: on 32bit Slackware 15.0 and -current, all Chromium based programs will crash with a seccomp error. This is caused by the changes in glibc with regard to secure computing (seccomp), and the affected versions of glibc can be found in Slackware 15.0 and newer. The Chromium developers have been unable to update their sourcecode to make this work on 32bit Operating Systems. As a result, for instance Falkon on 32bit Slackware 15.0 and newer will crash immediately on startup.
The workaround is to disable the seccomp filter sandbox for your 32bit OS. This is achieved without much effort, you have to make an environment variable available after login: QTWEBENGINE_CHROMIUM_FLAGS needs to be set to “--disable-seccomp-filter-sandbox“.
For bash-compatible shells you would do as follows:
# echo "export QTWEBENGINE_CHROMIUM_FLAGS='--disable-seccomp-filter-sandbox'" > /etc/profile.d/chromium_seccomp.sh
# chmod +x /etc/profile.d/chromium_seccomp.sh
And after logging in again, you should find that calibre works also on 32bit Slackware.
Addendum: even the screenreader works. Right-click the current page in your open e-book text and then click “Read Aloud“. The text-to-speech is provided by an embedded speech-dispatcher program. Unfortunately the configuration button does not work there, but if you don’t like the default espeak voice you can manually pick one of the available alternatives by editing the file “/usr/lib64/calibre/etc/speech-dispatcher/speechd.conf” (on 32bit Slackware the libdir is ‘lib‘ of course).
Have fun! Eric
 The Chromium version has reached a triple-digit number: I have uploaded new packages for Chromium 100 (Slackware 14.2 and newer, 32bit as well as 64bit). Specifically it is the release 100.0.4896.60 which was announced a few days ago. It fixes a number of vulnerabilities with the criticality label “high” which usually means it can crash your browser but not compromise your computer.
The Chromium version has reached a triple-digit number: I have uploaded new packages for Chromium 100 (Slackware 14.2 and newer, 32bit as well as 64bit). Specifically it is the release 100.0.4896.60 which was announced a few days ago. It fixes a number of vulnerabilities with the criticality label “high” which usually means it can crash your browser but not compromise your computer. Finally! I have a working package for Calibre 5.38.0, targeting Slackware 15.0 and -current.
Finally! I have a working package for Calibre 5.38.0, targeting Slackware 15.0 and -current.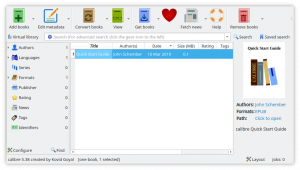
 I am considering an additional article to my
I am considering an additional article to my  I am happy with the Element app on Nextcloud, it allows me to talk to people in the Slackware Matrix room but also to connect to the
I am happy with the Element app on Nextcloud, it allows me to talk to people in the Slackware Matrix room but also to connect to the 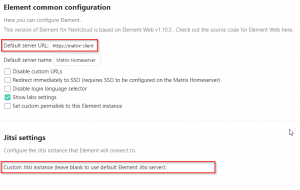
 But then I read the
But then I read the
Recent comments